Expo
view channel
view channel
view channel
view channel
view channel
view channel
view channel
RadiographyMRIUltrasoundNuclear MedicineGeneral/Advanced ImagingImaging IT
Events

- Simple Chest X-Ray Measure Predicts Survival After Lung Cancer Surgery
- AI Detection Tool Improves Identification of Lobular Breast Cancer
- New Contrast Agent Enables Low-Dose X-Ray Joint Imaging
- AI Boosts Breast Cancer Detection and Cuts Screening Workload
- AI Tool Predicts Breast Cancer Risk Years Ahead Using Routine Mammograms
- Cardiac MRI Measure Improves Risk Prediction in Tricuspid Regurgitation
- AI System Improves Accuracy of Cardiac MRI Interpretation
- Deep Learning Model Predicts Alzheimer’s Disease Outcomes from Baseline MRI
- AI Body Composition MRI Analysis Predicts Cardiometabolic Disease Risk
- Blood-Brain Barrier Imaging Adds Risk Insight to Standard Stroke MRI
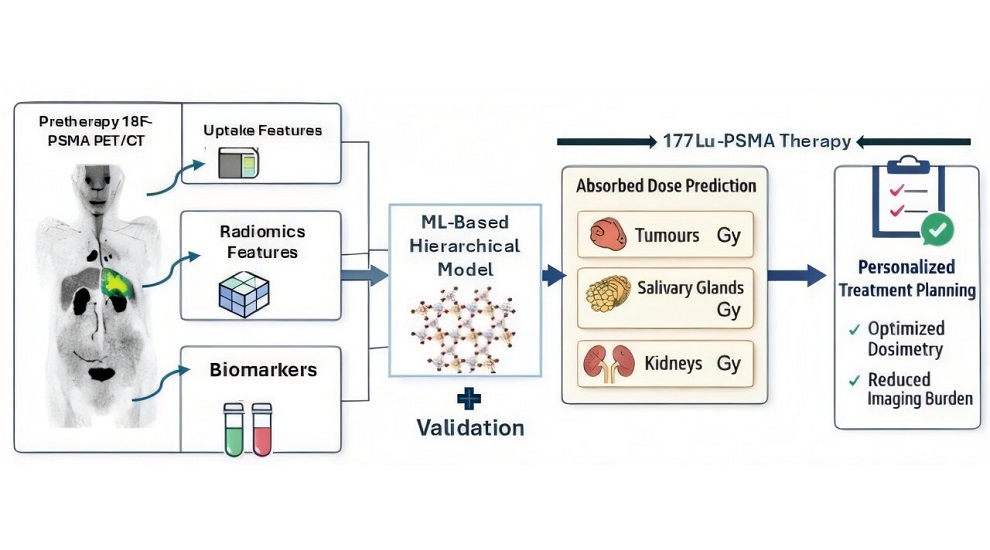
- AI Model Predicts Radiation Dose Before Prostate Cancer Therapy
- Vault-Free Radiosurgery Platform Expands Access to Cranial Tumor Care
- MR-Guided Cardiac Mapping System Enables Radiation-Free Procedures
- PET Tracer Enables Noninvasive Measurement of Beta Cell Mass
- New Imaging Tool Sheds Light on Tumor Fat Metabolism
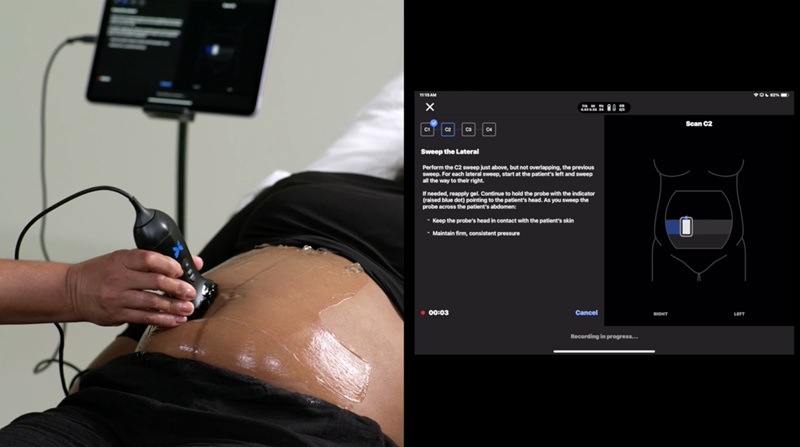
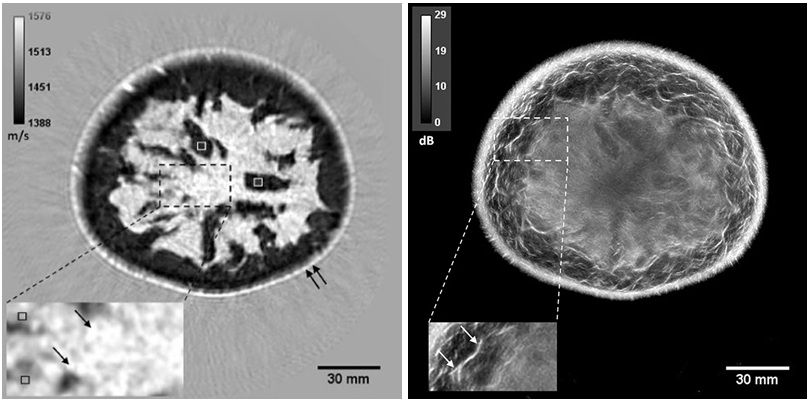
- Whole Cross-Section Ultrasound System Enables Operator-Independent Imaging
- New Ultrasound AI Tool Supports Rapid Prenatal Assessment
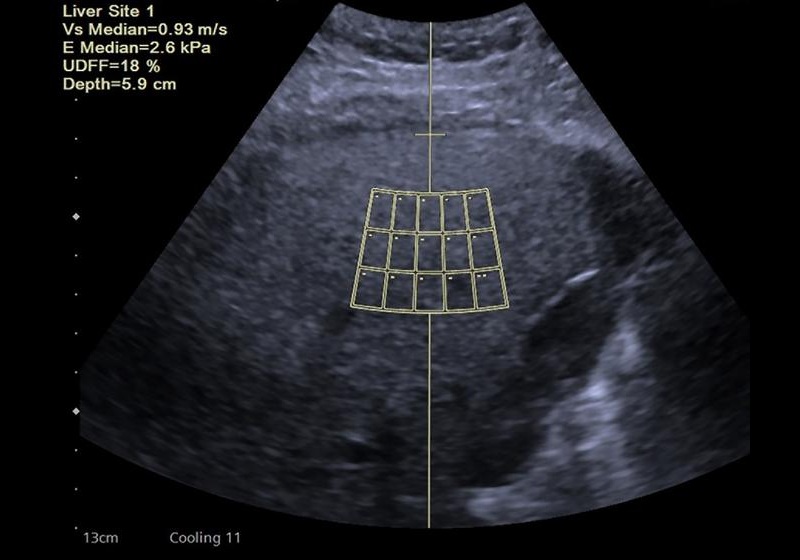
- New Consensus Standardizes Ultrasound-Based Fatty Liver Assessment
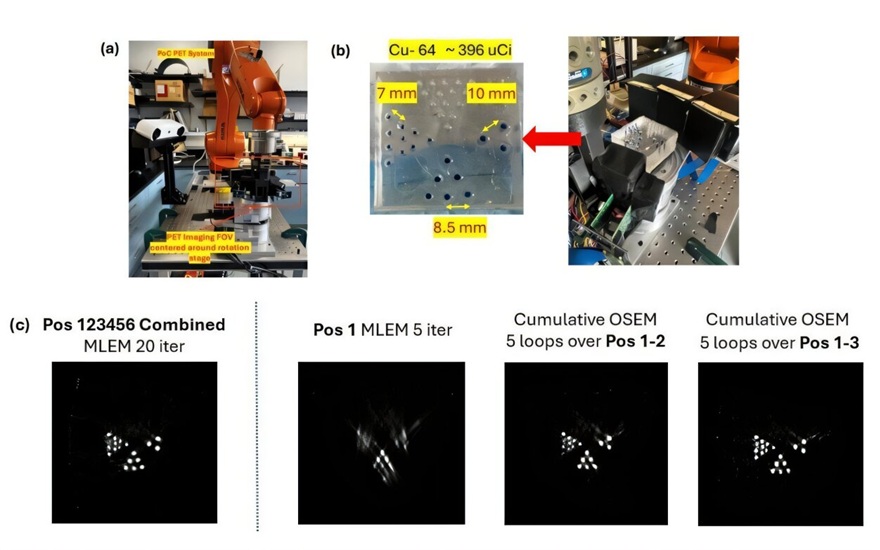
- Groundbreaking Technology to Enhance Precision in Emergency and Critical Care
- Reusable Gel Pad Made from Tamarind Seed Could Transform Ultrasound Examinations
- PET Tracer Localizes Overactive Adrenal Glands in Primary Aldosteronism
- Multimodal AI Tool Combines CT and Health Records to Predict Heart Risk
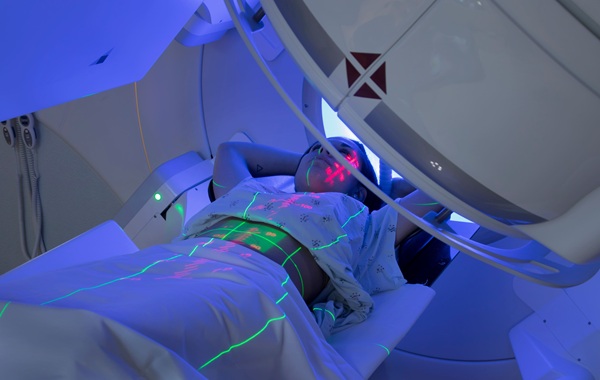
- AI Tool Automates Radiotherapy Planning for Cervical and Prostate Cancer
- New Proton Therapy Platform Integrates into Existing Radiotherapy Departments
- 3D-Printed Intraoral Device Enhances Head and Neck Radiotherapy Accuracy
- Breast Imaging Software Enhances Visualization and Tissue Characterization in Challenging Cases
- New Google Cloud Medical Imaging Suite Makes Imaging Healthcare Data More Accessible
- Global AI in Medical Diagnostics Market to Be Driven by Demand for Image Recognition in Radiology
- AI-Based Mammography Triage Software Helps Dramatically Improve Interpretation Process
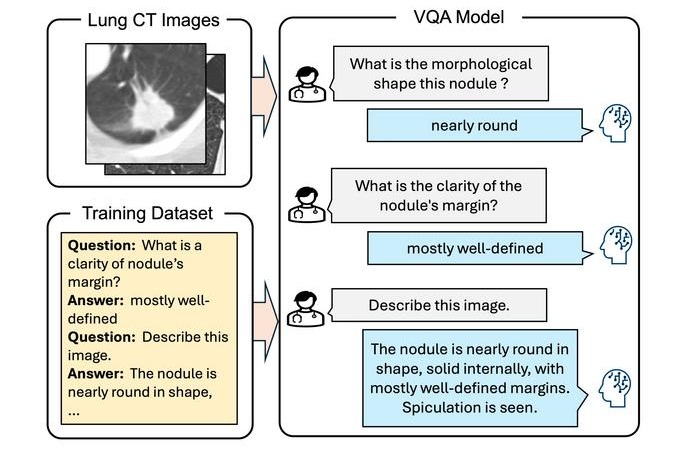
- Artificial Intelligence (AI) Program Accurately Predicts Lung Cancer Risk from CT Images
- GE HealthCare Highlights AI-Supported Radiation Therapy Tools at ESTRO 2026
- Nuclear Medicine Set for Continued Growth Driven by Demand for Precision Diagnostics
- GE HealthCare and NVIDIA Collaboration to Reimagine Diagnostic Imaging
- Patient-Specific 3D-Printed Phantoms Transform CT Imaging
- Siemens and Sectra Collaborate on Enhancing Radiology Workflows

 Expo
Expo
- Simple Chest X-Ray Measure Predicts Survival After Lung Cancer Surgery
- AI Detection Tool Improves Identification of Lobular Breast Cancer
- New Contrast Agent Enables Low-Dose X-Ray Joint Imaging
- AI Boosts Breast Cancer Detection and Cuts Screening Workload
- AI Tool Predicts Breast Cancer Risk Years Ahead Using Routine Mammograms
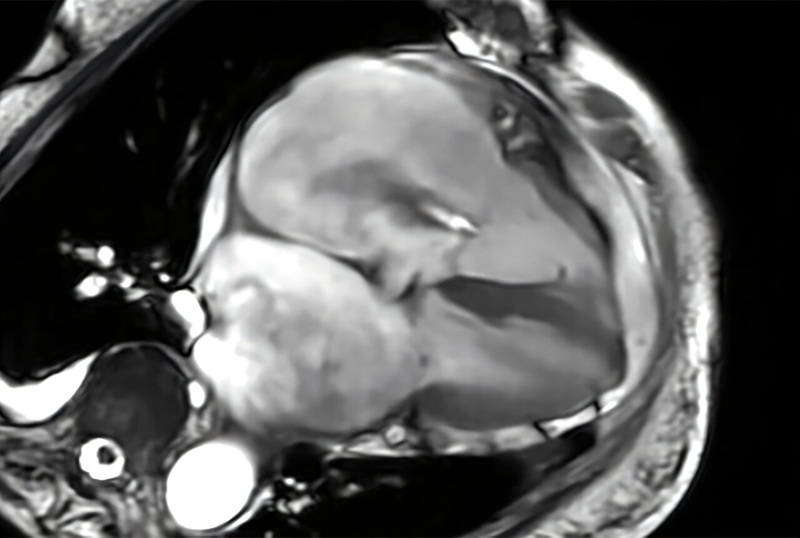
- Cardiac MRI Measure Improves Risk Prediction in Tricuspid Regurgitation
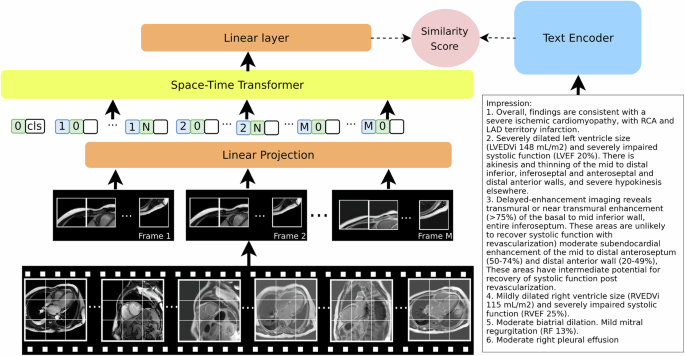
- AI System Improves Accuracy of Cardiac MRI Interpretation
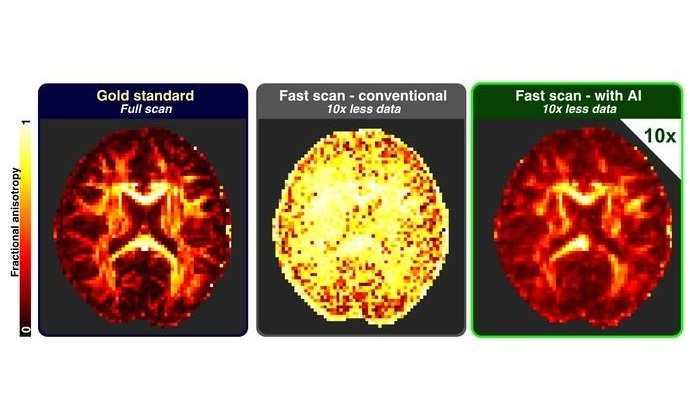
- Deep Learning Model Predicts Alzheimer’s Disease Outcomes from Baseline MRI
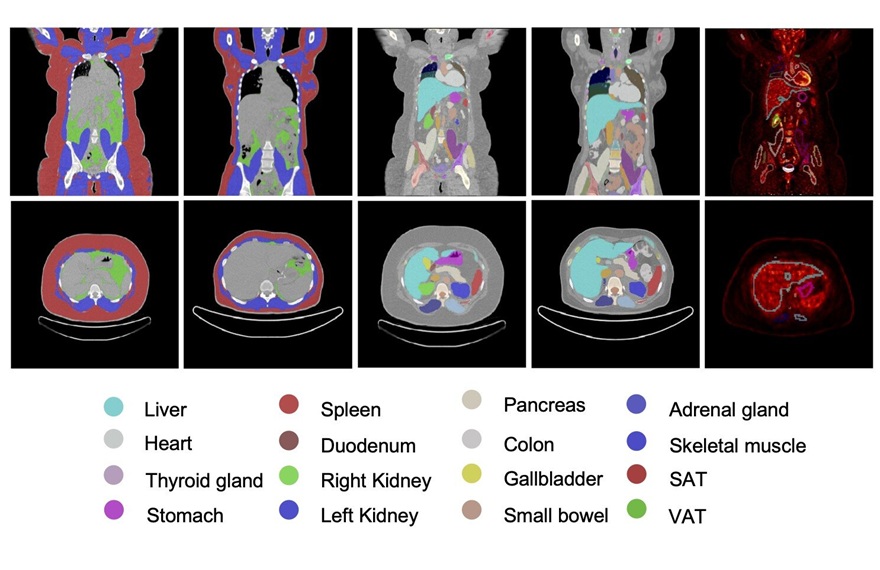
- AI Body Composition MRI Analysis Predicts Cardiometabolic Disease Risk
- Blood-Brain Barrier Imaging Adds Risk Insight to Standard Stroke MRI
- AI Model Predicts Radiation Dose Before Prostate Cancer Therapy
- Vault-Free Radiosurgery Platform Expands Access to Cranial Tumor Care
- MR-Guided Cardiac Mapping System Enables Radiation-Free Procedures
- PET Tracer Enables Noninvasive Measurement of Beta Cell Mass
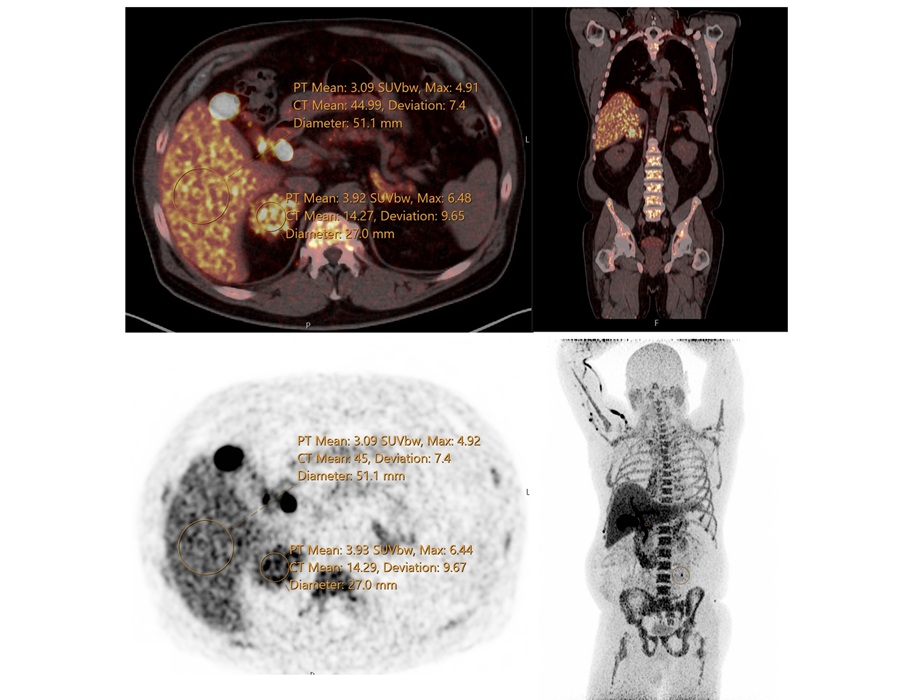
- New Imaging Tool Sheds Light on Tumor Fat Metabolism
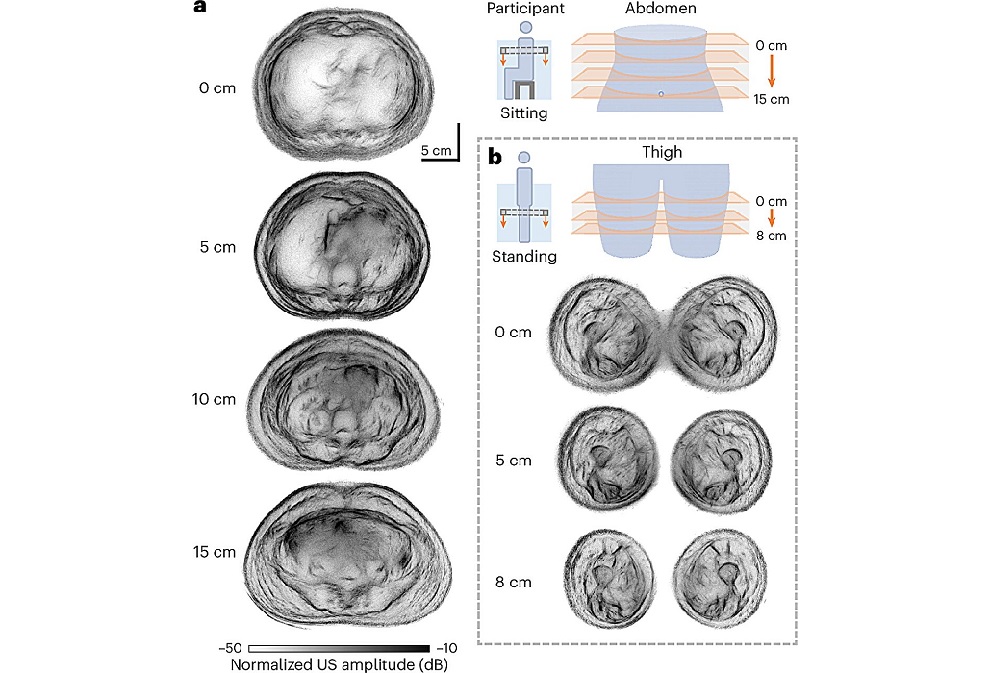
- Whole Cross-Section Ultrasound System Enables Operator-Independent Imaging
- New Ultrasound AI Tool Supports Rapid Prenatal Assessment
- New Consensus Standardizes Ultrasound-Based Fatty Liver Assessment
- Groundbreaking Technology to Enhance Precision in Emergency and Critical Care
- Reusable Gel Pad Made from Tamarind Seed Could Transform Ultrasound Examinations
- PET Tracer Localizes Overactive Adrenal Glands in Primary Aldosteronism
- Multimodal AI Tool Combines CT and Health Records to Predict Heart Risk
- AI Tool Automates Radiotherapy Planning for Cervical and Prostate Cancer
- New Proton Therapy Platform Integrates into Existing Radiotherapy Departments
- 3D-Printed Intraoral Device Enhances Head and Neck Radiotherapy Accuracy
- Breast Imaging Software Enhances Visualization and Tissue Characterization in Challenging Cases
- New Google Cloud Medical Imaging Suite Makes Imaging Healthcare Data More Accessible
- Global AI in Medical Diagnostics Market to Be Driven by Demand for Image Recognition in Radiology
- AI-Based Mammography Triage Software Helps Dramatically Improve Interpretation Process
- Artificial Intelligence (AI) Program Accurately Predicts Lung Cancer Risk from CT Images
- GE HealthCare Highlights AI-Supported Radiation Therapy Tools at ESTRO 2026
- Nuclear Medicine Set for Continued Growth Driven by Demand for Precision Diagnostics
- GE HealthCare and NVIDIA Collaboration to Reimagine Diagnostic Imaging
- Patient-Specific 3D-Printed Phantoms Transform CT Imaging
- Siemens and Sectra Collaborate on Enhancing Radiology Workflows